MetaDefender API http request object
V4 API is the latest version of MetaDefender Cloud API. It was designed to be fast, modular, easy to use and to provide seamless integration between MetaDefender API and MetaDefender Cloud API.
I will show how to call this API with several languages to SCAN a exe file.
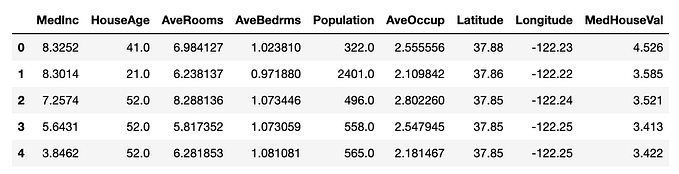
File Overview
Vendor kleiner kommunikation Product maXbox4 Category E Copyright Free Pascal Script File type Executable File File Extension exe File size 28 MB [29608248 bytes] Uploaded 2020–06–16 17:02:33 [ 2 months ago ] Scanned 2020–08–28 18:51:29 [ 2 hours ago ] Duration a few seconds
MD5 21648AFA06BEAD05E50D20D8BC0B67D9
SHA1 DA4C716E31E2A4298013DFFBDA7A98D48650B0C7
SHA256 E0CB57D978207D09A6849EFB0E972FD4D0B407A42F6EB891AB41E68B53785293
First we start with Pascal in maXbox. We use type THTTPSend = class(TSynaClient) from the unit HTTPSend.
function HTTPMethod(const Method, URL: string): Boolean;
Connects to host define in URL and access to resource defined in URL by method. If Document is not empty, send it to server as part of HTTP request. Server response is in Document and headers. Connection may be authorized by username and password in URL. If you define proxy properties, connection is made by this proxy. If all OK, result is True, else result is False.
If you use in URL ‘https:’ instead only ‘http:’, then your request is made by SSL/TLS connection (if you not specify port, then port 443 is used instead standard port 80). If you use SSL/TLS request and you have defined HTTP proxy, then HTTP-tunnel mode is automaticly used .
Before HTTP operation you may define any non-standard headers for HTTP request, except of: ‘Expect: 100-continue’, ‘Content-Length’, ‘Content-Type’, ‘Connection’, ‘Authorization’, ‘Proxy-Authorization’ and ‘Host’ headers. After HTTP operation contains full headers of returned document.
Stream with document to send (before request, or with document received from HTTP server (after request).
Const URL='https://api.metadefender.com/v4/file/bzIwMDYxNi1TSW42NDBPVlprTWw3YjRBMQ';
Begin //@main
srlist:= TStringlist.create;
with THTTPSend.create() do begin
Headers.Add('apikey: 6b337c92c792174a54acd715ab1aae64');
writeln(botostr(HTTPMethod('GET',URL)));
with TJson.create() do begin
Parse(StreamtoString3(Document));
Split(Stringify,'{',srlist)
end;
writeln(itoa(resultCode)+':'+resultString+CRLF+srlist.text);
clear;free;
end;
srlist.Free; //withParent class of application protocol implementations. By this class is defined common properties.
Next we do the same with Python:
import requests
url = "https://api.metadefender.com/v4/file/bzIwMDYxNi1TSW42NDBPVnJJb0p1WTZWYTY"
headers = { 'apikey': "6b337c92c792174a54acd715ab1aae64" }
response = requests.request("GET", url, headers=headers) print(response.text)For a better understanding of the difference between V4 and previous versions of the API, see: V4 Migration guide.
Another solution is from Microsoft Windows HTTP Services (WinHTTP) which provides developers with an HTTP client application programming interface (API) to send requests through the HTTP protocol to other HTTP servers.
WinHTTP supports desktop client applications, Windows services, and Windows server-based applications.
// Instantiate a WinHttpRequest object.
httpReq:= CreateOleObject('WinHttp.WinHttpRequest.5.1');
// Open an HTTP connection.
hr:= httpReq.Open('GET', aURL, false);
if hr= 0 then
httpReq.setRequestheader('apikey','6b337c92c792174a54acd715ab1aae64'); httpReq.Send() /// Send HTTP Request & get Responses. writeln(httpReq.responseText)
writeln(httpReq.GetAllResponseHeaders());
httpReq:= NULL; //closeDeprecation notice
All previous version of the API (V1, V2, and V3) will be deprecated in Feb 1st, 2020. Please make sure to update your code to use the latest version of the API. V4 will be supported for a minimum of 3 years since the date of its announcement (March 2019).
And in the last step with CURL:
curl 'https://api.metadefender.com/v4/file/bzIwMDYxNi1TSW42NDBPVnJJb0p1WTZWYTY' \ -H 'apikey: 6b337c92c792174a54acd715ab1aae64'Functions and Procedures
function HttpGetText(const URL: string; const Response: TStrings): Boolean;
function HttpGetBinary(const URL: string; const Response: TStream): Boolean;
function HttpPostBinary(const URL: string; const Data: TStream): Boolean;
function HttpPostURL(const URL,URLData: string; const Data: TStream): Boolean;
function HttpPostFile(const URL,FieldName,FileName: string; const Data: TStream; const ResultData: TStrings): Boolean;
Note: The apikey is used for all API request to MetaDefender Cloud service. A Web Request or SendRequest can pass a request header to do that and control the response header too, for example the X-Authenticated: by apikey :
1.0 HTTP/1.1 200 OK
Date: Sat, 29 Aug 2020 10:39:58 GMT
Content-Type: application/json; charset=utf-8
Content-Length: 5294
Connection: keep-alive
Strict-Transport-Security: max-age=63072000; includeSubDomains; preload
Vary: Accept-Encoding, Origin
X-Authenticated: by apikey
X-Account-Type: anonymous
X-Content-Type-Options: nosniff
ETag: “14ae-6IDbUoWEYrVD4MsFYbhiMMsZWIM”
X-Response-Time: 648ms
Cerber ransomware was found in March 2016 and actually It is being offered as Ransomware-as-a-Service on Russian forums so pretty much anyone can use it without coding experience.
The hackers get victims to download Cerber with two methods; first is a double-zipped file with a WSF (Windows Script File) inside attached to the malicious email, the second is an unsubscribe link located at the bottom of the phishing email, which also links to the same ZIP file. This new strain was also pushed by the Rig and Magnitude exploit kits which both are using 0-day vulnerabilities.
Originally published at http://maxbox4.wordpress.com on September 1, 2020.